Counter productive: cyber security agencIES Bureaucrats


---Begin forwarded message:
Date: Sep 2025
To: amorn.c@ncsa.or.th, Jadet.k@ncsa.or.th
To: "Sihasak Phuangketkeow " S.Phuangketkeow@thaigov.go.th, protocol02@mfa.go.th
Subject: [คําเตือน]: NSCA และ NCSC กําลังถูกสอดแนมและเยี่ยมชมโดยแฮกเกอร์อาชญากรโดยที่พวกเขาไม่รู้ตัว
Dear NCSA Leaders Amorn and Jadet,
I've been having a conversation with one of your key people during the past many months.
It
started during a research project after i noticed that the Thai state
vital infrastructure security has far too many basic security flaws and
high-risk data leaks, and thus also long term ongoing infiltration for
espionage & sabotage by hostile actors.
During the conversations, while looking at a lot of evidence the past months, we came to the conclusion: that
the source of that high-risk state security problem is actually "How"
NCSA staff and the Thai military staff are far too "Top-down
Hierarchical*" and thus unable to accept well intended advice and
comments which maybe seen like 'criticism' on choices that have been
made by high ranking officials.
* When comparing the Thai security structure with for
instance the Cambodian current structure, it is blatantly obvious that
the Thai security core risk-management structure is lagging very far
behind..
Various essential simple (no extra costs!!)
security measures are clearly not enforced by the Thai govt
NCSA/CERT/NCSC/CRC/CMO/ETDA/.. organisations, which means that there are
far too many required protection measures not actually done, leaving
big gaps for intruders and sabotage. [* กำแพงมีหู ประตูมีช่อง *]
Key example is:
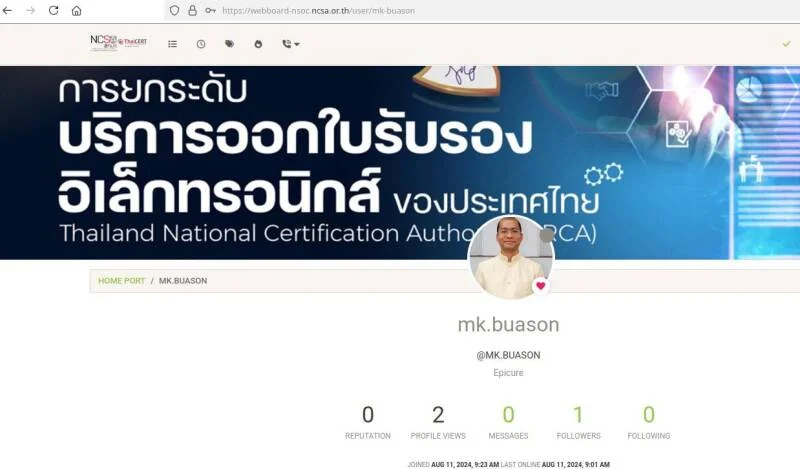
https://webboard-nsoc.ncsa.or.th/admin **
https://webboard-nsoc.ncsa.or.th/category/26/training
https://webboard-nsoc.ncsa.or.th/topic/2175/cyber-threat-intelligence-08-september-2025
That
ICT system which is supposed to show that NCSA is leading by
example..., is instead clearly showing to the world that the NCSA
Thailand can't even take care of the own systems and data protection!
Even
basic well known security measures rules seem to be just ignored {{the
"quick and careless"(Q&C) method was used to build and operate that
service + the NCSA emails service}}, thus it seems like no one actually
really cares that hostile actors also have access for a long time and
use various NCSA IT related systems to deeply Profile state security and
manipulate key security functionaries within NCSA & NCSC and other
govt cells to do the wrong things ..further undermine state security
even more. *sigh*
There is a lot of security sensitive information
floating around "unprotected" in Thai Govt Systems, and it keeps getting
in the hands of various hostile actors for some years now. So they know
exactly: where to go, who and what to target, and "How".
-
รำไมดีโทษปี่โทษกลอง - There isn't even a functional "Data Classification
Policy" created by Thailands NCSA/NCSC/CRC/CMO/ETDA/.etc., so no solid
foundation to build a functional security structure on :(
#Observation:
There are various official Thai 'security policy' and other official
documents; & various Thai Govt & Mil & Vital Infrastructure
ICT systems; which clearly showcase that the currently used ''security''
structure is blatantly failing on various levels. Something that would
need to be fixed a.s.a.p. in order provide actual functional protection.
^^ The key question now is: Do you, as the current NCSA Leaders, actually want to put a bit of effort into Fixing the Thai state security structure? To make self-evidently sure that Thailand govt gets ahead on not only Cambodian govt & mil, but also several others..
B) If "no": Why not .?.
A) If "yes": Then it seems clear that a change in tactics is needed ~
By
NCSA & NCSC staff wanting to _Learn_ "How" to run a security
organisation which can lead by example and actually obtain the required
"knowledge and power" to make absolutely proven sure that the Thai state
infrastructure is managed in a way that is actually compliant with
common sense protection regulations.
It only takes about 3 weeks to
transfer the needed knowledge and show how to use it with your own
people. This isn't a commercial offer, its just a gesture of good will
to help out where most needed.
If you both actually want do want to
learn "how" to fix the security structure problem(s), then we are
willing to give the essential training/education for the benefit of the
overall population.
Kindest regards,
*******
Operational Chief Security Officer. (OCSO)
---
Note: The reason why we have chosen that i will contact
you, instead of the local person who has been working with your
organisation for some time.
That is mentioned at the beginning of
this letter; so that person naturally doesn't dare to speak up, in fear
that some higher ranking grumpy official will act offended and
'retaliate' / Instead of all together having open-minded dialog's about
"How" to best correct some wrong core choices made in the past, to move
forward together with a functional method.
No one needs to be blamed
for 'wrong' choices anyway, because they happen due to understandable
circumstances at that time in the past and may have seemed like to
correct option at that time. => Live and learn together, from all the progressive insight we can get from learning from anyone who cares to share theirs.
"Do not esteem highly those who praise all your words and deeds, but those who sincerely point out your mistakes.."
> Socrates, ~2500 years ago.
# ----------\
Date: Sep 2025
From: AVM Jadet Khuhakongkit <jadet.k@ncsa.or.th>
To: ****** , Amorn Chomcheay <amorn.c@ncsa.or.th>
Subject: Re: [คําเตือน]: NSCA และ NCSC กําลังถูกสอดแนมและเยี่ยมชมโดยแฮกเกอร์อาชญากรโดยที่พวกเขาไม่รู้ตัว
Dear ****,
Thank you very much for your suggestions to NCSA. Kindly provide more specific and detailed information so that NCSA can efficiently implement improvements. We greatly appreciate your cooperation and the valuable feedback that helps enhance our operations.
Best regards,
Air vice marshal Jadet Khuhakongkit
Assistant Secretary General, Deputy Director of ThaiCERT
National Cyber Security Agency (NCSA)
CISSP, CGRC, CC, Certified IRCA ISO/IEC 27001 Internal Auditor, CEH, Pentest+, CySA+, CASP+, Cloud+, Security+
Email: jadet.k@ncsa.or.th, Phone: +6625027804
# ----------\
Sep 2025
To: AVM Jadet Khuhakongkit <jadet.k@ncsa.or.th>
To: amorn.c@ncsa.or.th
Dear Jadet, [Air vice marshal; ''CISSP, CGRC, CC, Certified IRCA
ISO/IEC 27001 Internal Auditor, CEH, Pentest+, CySA+, CASP+, Cloud+,
Security+, etc..'' ;))
Thank you kindly for your quick reply.
Side Remark: As someone who isn't part of your hierarchical culture structure, one can freely point at various things which are obviously going very wrong and/but can be fixed simply with the far more pragmatic "Safeguard" methodology.
Sadly, it seems like you still prefer sending a "Default response text" (a copy & paste text from some apathetic NCSC's elsewhere), ..which is obviously missing any of the required substance based on the described actual situation. *sigh*
That seems a bit like:
1) a chief fireman getting a SMS message to
his work phone on วันอาทิตย์ 03:00 AM, while he is at home in bed:
"There is a lot of black smoke and flames coming out of the top window
of your Fire Station building in town!, but the building fire alarm did
not go off and there is no fireman here now."
2) that chief fireman
only responding with a SMS stating: "Oh really, before i will do
anything about it _you_ will have to describe in more detail what you
think is going on there.". ..and then just going back to sleep again.
หนึ่ง) If you actually want more "specific and detailed information",
then of course you yourself need to state "which specific information"
you are after, in context to which item(s) listed in the message send to
you.
Else i would have to guess, which of the various security
issues are already known to you, and which are still outside your realm
of awareness or caring -> ?
Even the mere fact that you as chief 'security specialist' with all
those *Theoretical* Certifications, as spokesperson of The NCSA.go.th,
are asking people to send you specific details about active Security
Flaws in the Thai State infrastructure, via PUBLIC internet email
servers ==> Without.. arranging the required mandatory
person-to-person(P2P) Encryption (like with PGP) to simply Protect such
classified information from getting into the wrong hands..
That
intriguing situation does say a lot about the urgent need for real
"operational" security awareness and capabilities Training, for you and
your colleagues, doesn't it ?
สอง) If you actually want to Resolve the high-risk security
issues caused by NCSA Th itself, then you clearly need to have a open
minded Dialog about what is described.
Which means that you pick the
subjects you want to further discuss by mentioning your point of view
on it. Then we can progress further on it.
One of your cooperatives has already made it clear that NCSA is fully
aware that your are many miles behind, even on your southern neighbour
country, when it comes to "actually getting security measures
implemented".
Which means that it is well known that there is a
structural Core problem with NCSA's/(mod.go.th) capability to get
security measures actually done..
Root cause of that lack of
"Accomplishing Enforcement Power" comes from the fact that NCSA&NCSC
go.Th is using a far too bureaucratic methodology. Too much focused on
office paperwork: describing policies which obviously lack some
essential key details; ticking check-lists without actually checking if
its all really done => turning a blind eye when security measures are
not actually done due to *favouritism/cronyism*.
=> # en.wikipedia.org/wiki/Paper_tiger
# Lets take one telling example from a rather long list of observed security and compliance flaws/issues:
NCSA is supposed to Lead By Example, when it comes to doing functional 'security'. Doesn't it !?
?
How come, that there are still several IT systems which are internet
connected, used by NCSA, to handle partly classified security sensitive
information, ..but clearly are not even complaint with basic common
sense security rules and regulations !?
Like that webboard-nsoc.ncsa.or.th service:
Which person has chosen to even allow "Admin" rights Remote Access to NCSA services, to start with !?
Even
Single factor lazy authentication is allowed, without basic
(multi-factor) and common sense Verification of Authorisation Identity
and origin.
And also allow account password reset via Public email
services, which can also be accessed/intercepted by foreign hostile
actors and local common criminals. Since even you are using the
*external* and known rather vulnerable "webmail.workd.go.th" to handle
such NCSA.govt security emails, ..it is of course made possible by
yourself for criminals and hostile actors to intercept/redirect those
security details without you even ever noticing it. That is basic
knowledge also you have read about during all your certifications, isn't
it?
# Dear Jadet, it is a serious question for you to think about: Are you able to name the person who has officially "allowed" it in writing that essential elementary security rules/regulations may be ignored ? Thus hostile actors implicitly 'may' also have access to high-risk state security related (secret) information, without any need to allow such uncontrolled access !?
[webboard-nsoc.ncsa.or.th]
สาม~ lacks decent hardening
*
which Cloudflare USA company proxies really can Not fix for you, of
course!, because Cloudflare does allow traffic to pass trough to the
vulnerable back-end actual NCSA servers]
สี่~ lacks functional intrusion prevention/detection.
*
even allows 'visitors' from China,Russia,USA,Cambodia,etc to enter and
go trough all the NCSA/mod.go.th sensitive information in there.
*
the Web service even Allows the listing of *all* the registered users
and their information. Which one normally would consider to also be a
high-prio security data breach/leak incident, to be fixed/resolved
within 8 hours.
* who can and will actually Detect it when those
ongoing NCSC security vulnerabilities updates/publications have been
tampered with (modified) by unauthorised 'visitors'?
* ...
ห้า~ clearly seems like no one is actually Enforcing a decent functional "Data Classification Policy".
*
because various people (including officers like Monkolc, CERT &
NCSC members, and various others) are recklessly sharing sec sensitive
information about themselves and state security structures to the public
and hostile forces!
=> Which means that NCSA 'allows' them to make themselves and the state Extra Vulnerable for:
- Profiling*;
- Bribes/Blackmail;
- Social Engineering / manipulation;
- Targeted hackers attacks with very specific target 'knowledge';
- Interception of secret communication;
- ... ;
- ..and various other known security undermining methods..
หก .. สิบ~ [Classified details], we could better talk about in person, if you do care to arrange a few meetings to facilitate things to happen.
But, that is just about 1 of the NCSA's own services, there are too
many other *.go.th infrastructure items which have clearly both
digitally and physical location serious lack of common sense functional
protection.
~ Which makes it seem like NCSA management is still
working from a Ivory Tower perspective, instead of doing the essential
Functional hands-on tasks required to ensure actually pragmatic State
Vital Infrastructure Protection. :(
FYI:
With the right "operational" security methodology knowledge
injection, yourselves can become capable to quickly make sure that NCSA
can actually "lead by example" to ensure a proven fully functioning
Safeguard/security structure.
Remark: Of course its known that it is
Thai cultural difficult to accept the need for external help when in a
position of senior leadership or just higher ranking, ...but if you can
just accept the fact that there is clearly the urgent need for such a
knowledge transfer into your organisation, and thus to allow yourselves
to be open-minded about Learning some key things which are specifically
''deliberately'' Not mentioned in those far too theoretical/bureaucratic
official (USA origin) guidelines like: [''CISSP, CGRC, CC, Certified
IRCA ISO/IEC 27001 Internal Auditor, CEH, Pentest+, CySA+, CASP+,
Cloud+, Security+''].
As mentioned before, this conversation and knowledge transfer
offer, is just intended to Help NCSA Thai state security for the benefit
of the Thai Population. As requested by one of your go.th connected snr
officials.
It's up to you as NCSA functionaries to choose to do the
right thing for everyone, by factually wanting to improve the protection
of Thailand by actually wanting to Learn about 'outside-the-box'
Risk-Management Structure options. Isn't it ?
NCSA/NCSC/CERT go.th
still has a lot of catching up to do when it comes to Learning how to
run a Functional Security Authority organisation which clearly proves
real tangible results.
If you care to just arrange all that is needed to have a series of confidential open-minded friendly conversations about it, if you do want to resolve the ongoing NCSA dilemma once and for all.
ด้วยความเคารพ | With kind regards
****.
/---!*!---\
> From: Amorn Chomcheay <amorn.c@ncsa.or.th>
> Subject: Read:
> Your message
> To: Amorn Chomcheay
> Subject: กำแพงมีหู ประตูมีช่อง *
>
> * was read on Saturday, ..... PM (UTC+07:00) Bangkok,
>
> Disposition: automatic-action/MDN-sent-automatically; displayed
> X-MSExch-Espionage-Profiling-Correlation-Key: X4..........g==
> X-Display-Name: Amorn Chomcheay
> --
> Importance: high
> X-Priority: 1
> Return-Path: <amorn.c@ncsa.or.th>
> !** Received: from webmail.workd.go.th (49.229.91.134)
> Received: from TY2PEPF0000AB89.apcprd03.prod.outlook.com (2603:1096:300:59:cafe::33) by PS2PR02CA0027.outlook.office365.com
> !
* Received: from DGAEX06MB.workd.local (10.20.10.156) by
DGAEX08MB.workd.local (10.20.10.158) with Microsoft SMTP Server
(version=TLS1_2, cipher=TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384) id
15.2.1748.10 [!* MS-Exchange Server v2019 CU15 Jan-25 KB5042461 *!]
> Received: via [40.107.75.140], from DGAEX06MB.workd.local ([fe80::6247:339:884d:5074])
> !
* X-MS-Exchange-Authentication-Results: spf=pass (sender IP is
49.229.91.134 {AIS Network Management Center, Bangkok})
smtp.mailfrom=ncsa.or.th; dkim=none (message not signed!)
> ARC-Message-Signature: i=1; a=rsa-sha256; c=relaxed/relaxed; d=microsoft.com; s=arcselector10001;
>
smtp.mailfrom=ncsa.or.th; dmarc=pass; (p=reject sp=reject pct=100)
action=none header.from=ncsa.or.th; dkim=none; (message not signed);
arc=none (0)
> X-MS-Exchange-SenderADCheck; X5hsjXwAPfYyN9CWVFtErkzOnhPTkBEDQd2gLoelq6x=
> Microsoft SMTP Server (version=TLS1_2, cipher=TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384) id !!* v15.20.9137.16 *!!
> X-MS-PublicTrafficType: Email
> X-MS-TrafficTypeDiagnostic: TY2PEPF0000AB89:EE_|SEZPR06MB5854:EE_
> X-MS-Exchange-CrossTenant-AuthSource: TY2PEPF0000AB89.apcprd03.prod.outlook.com
> !** X-MS-Exchange-CrossTenant-Id: 3a805853-fd60-448e-812e-0558b4bc813c <== *!
> !*** X-MS-Exchange-CrossTenant-FromEntityHeader: HybridOnPrem
> etc..
> etc...
webmail.workd.go.th (49.229.91.134)
25/tcp open smtp Microsoft Exchange smtpd
|
smtp-commands: DGAEX09MB.workd.local Hello, SIZE 50331648, PIPELINING,
DSN, ENHANCEDSTATUSCODES, STARTTLS, X-ANONYMOUSTLS, AUTH NTLM, X-EXPS
GSSAPI NTLM, 8BITMIME, BINARYMIME, CHUNKING, SMTPUTF8, XRDST
|_ This server supports the following commands: HELO EHLO STARTTLS RCPT DATA RSET MAIL QUIT HELP AUTH BDAT
|
ssl-cert: Subject: commonName=*.workd.go.th/organizationName=Digital
Government Development Agency (Public
Organization)/stateOrProvinceName=Bangkok/countryName=TH
| Subject Alternative Name: DNS:*.workd.go.th, DNS:workd.go.th
| Issuer: commonName=DigiCert Global G2 TLS RSA SHA256 2020 CA1/organizationName=DigiCert Inc/countryName=**US!!
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-09-09T00:00:00
| Not valid after: 2025-10-09T23:59:59
| MD5: 7914:4424:0c9a:0344:0e93:0e30:e660:7c99
|_SHA-1: b96c:a8d4:f49a:3f47:352f:74c8:4d6a:b68f:f863:7b25
80/tcp open http Microsoft IIS httpd 10.0
|_http-server-header: Microsoft-IIS/10.0
110/tcp open pop3 Microsoft Exchange 2007-2010 pop3d
|
ssl-cert: Subject: commonName=*.workd.go.th/organizationName=Digital
Government Development Agency (Public
Organization)/stateOrProvinceName=Bangkok/countryName=TH
| Subject Alternative Name: DNS:*.workd.go.th, DNS:workd.go.th
| Issuer: commonName=DigiCert Global G2 TLS RSA SHA256 2020 CA1/organizationName=DigiCert Inc/countryName=**US!!
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-09-10T00:00:00
| Not valid after: 2026-10-11T23:59:59
| MD5: e4b6:aece:822f:1038:d74d:f68c:c4dd:5864
|_SHA-1: bd27:c192:2571:d6d9:eda0:7fab:bb66:008a:599d:7516
|_pop3-capabilities: UIDL TOP STLS
143/tcp open imap Microsoft Exchange 2007-2010 imapd **!!!
| ssl-cert: Subject: commonName=*.workd.go.th/organizationName=Digital Government Development Agency (Public Organization)/stateOrProvinceName=Bangkok/countryName=TH
| Subject Alternative Name: DNS:*.workd.go.th, DNS:workd.go.th
| Issuer: commonName=DigiCert Global G2 TLS RSA SHA256 2020 CA1/organizationName=DigiCert Inc/countryName=US
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-09-09T00:00:00
| Not valid after: 2025-10-09T23:59:59
| MD5: 7914:4424:0c9a:0344:0e93:0e30:e660:7c99
|_SHA-1: b96c:a8d4:f49a:3f47:352f:74c8:4d6a:b68f:f863:7b25
| imap-ntlm-info:
| Target_Name: WORKD
| NetBIOS_Domain_Name: WORKD
| NetBIOS_Computer_Name: DGAEX32MB **!!
| DNS_Domain_Name: workd.local
| DNS_Computer_Name: DGAEX32MB.workd.local
| DNS_Tree_Name: workd.local
|_ Product_Version: 10.0.17763 **! [Known Vulnerable !!]
|
_imap-capabilities: NAMESPACE ID IDLE LITERAL+A0001 OK MOVE completed
CAPABILITY UNSELECT IMAP4rev1 SASL-IR STARTTLS IMAP4 UIDPLUS CHILDREN
LOGIN
443/tcp open ssl/https
| ssl-cert: Subject:
commonName=*.workd.go.th/organizationName=Digital Government Development
Agency (Public Organization)/stateOrProvinceName=Bangkok/countryName=TH
| Subject Alternative Name: DNS:*.workd.go.th, DNS:workd.go.th
| Issuer: commonName=DigiCert Global G2 TLS RSA SHA256 2020 CA1/organizationName=DigiCert Inc/countryName=US
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-09-09T00:00:00
| Not valid after: 2025-10-09T23:59:59
| MD5: 7914:4424:0c9a:0344:0e93:0e30:e660:7c99
|_SHA-1: b96c:a8d4:f49a:3f47:352f:74c8:4d6a:b68f:f863:7b25
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
| http-title: Sign In
**!! |_Requested resource was https://sts.workd.go.th/adfs/ls/?wa=wsignin1.0&wtrealm=https%3a%2f%2fwebmail.workd.go.th%2fowa%2f&wctx=rm%3d0%26id%3dpassive%26ru%3d%252fowa%252f
|_http-server-header: Microsoft-IIS/10.0 *!!
|_http-favicon: favicon MD5: F99E4DB581EFAF34D8AF63B0E270CEBF
587/tcp open smtp Microsoft Exchange smtpd
| smtp-ntlm-info:
| Target_Name: WORKD
| NetBIOS_Domain_Name: WORKD
| NetBIOS_Computer_Name: DGAEX17MB
| DNS_Domain_Name: workd.local
| DNS_Computer_Name: DGAEX17MB.workd.local
| DNS_Tree_Name: workd.local
|_ Product_Version: 10.0.17763 **!!
| ssl-cert: Subject:
commonName=*.workd.go.th/organizationName=Digital Government Development
Agency (Public Organization)/stateOrProvinceName=Bangkok/countryName=TH
| Subject Alternative Name: DNS:*.workd.go.th, DNS:workd.go.th
| Issuer: commonName=DigiCert Global G2 TLS RSA SHA256 2020 CA1/organizationName=DigiCert Inc/countryName=US
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-09-09T00:00:00
| Not valid after: 2025-10-09T23:59:59
| MD5: 7914:4424:0c9a:0344:0e93:0e30:e660:7c99
|_SHA-1: b96c:a8d4:f49a:3f47:352f:74c8:4d6a:b68f:f863:7b25
|
smtp-commands: webmail.workd.go.th Hello, SIZE 50331648, PIPELINING,
DSN, ENHANCEDSTATUSCODES, STARTTLS, AUTH GSSAPI NTLM, 8BITMIME,
BINARYMIME, CHUNKING, SMTPUTF8
|_ This server supports the following commands: HELO EHLO STARTTLS RCPT DATA RSET MAIL QUIT HELP AUTH BDAT
993/tcp open imaps?
| imap-ntlm-info:
| Target_Name: WORKD
| NetBIOS_Domain_Name: WORKD
| NetBIOS_Computer_Name: DGAEX31MB **!!!
| DNS_Domain_Name: workd.local
| DNS_Computer_Name: DGAEX31MB.workd.local
| DNS_Tree_Name: workd.local
|_ Product_Version: 10.0.17763
|
ssl-cert: Subject: commonName=*.workd.go.th/organizationName=Digital
Government Development Agency (Public
Organization)/stateOrProvinceName=Bangkok/countryName=TH
| Subject Alternative Name: DNS:*.workd.go.th, DNS:workd.go.th
| Issuer: commonName=DigiCert Global G2 TLS RSA SHA256 2020 CA1/organizationName=DigiCert Inc/countryName=US
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-09-09T00:00:00
| Not valid after: 2025-10-09T23:59:59
| MD5: 7914:4424:0c9a:0344:0e93:0e30:e660:7c99
|_SHA-1: b96c:a8d4:f49a:3f47:352f:74c8:4d6a:b68f:f863:7b25
|
_imap-capabilities: OK completed CAPABILITY IMAP4 CHILDREN IDLE ID
UIDPLUS AUTH=GSSAPI NAMESPACE SASL-IR UNSELECT LITERAL+A0001 AUTH=PLAIN
IMAP4rev1 AUTH=NTLM MOVE
995/tcp open pop3s
| ssl-cert: Subject:
commonName=*.workd.go.th/organizationName=Digital Government Development
Agency (Public Organization)/stateOrProvinceName=Bangkok/countryName=TH
| Subject Alternative Name: DNS:*.workd.go.th, DNS:workd.go.th
| Issuer: commonName=DigiCert Global G2 TLS RSA SHA256 2020 CA1/organizationName=DigiCert Inc/countryName=US
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-09-09T00:00:00
| Not valid after: 2025-10-09T23:59:59
| MD5: 7914:4424:0c9a:0344:0e93:0e30:e660:7c99
|_SHA-1: b96c:a8d4:f49a:3f47:352f:74c8:4d6a:b68f:f863:7b25
|_pop3-capabilities: UIDL TOP SASL(PLAIN) USER
Service Info: Hosts: DGAEX01MB.workd.local, webmail.workd.go.th; OS: Windows; CPE: cpe:/o:microsoft:windows
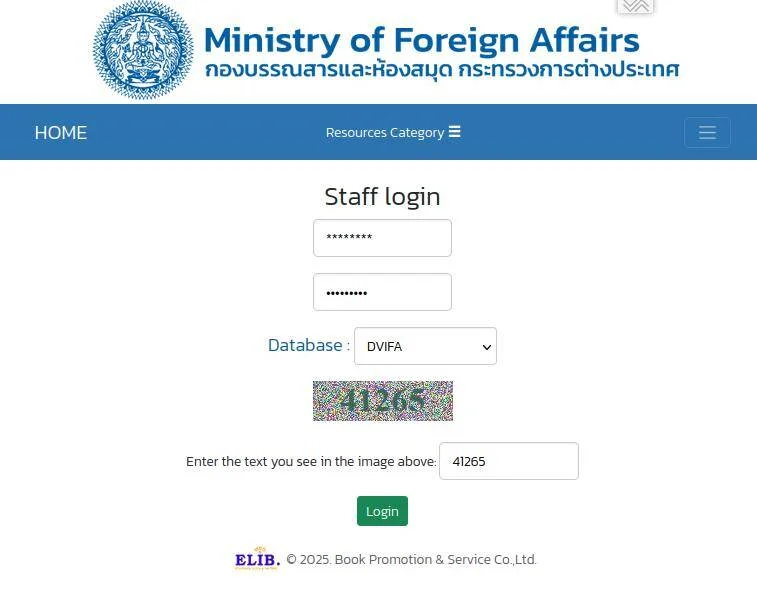
:( This publication and various
others (incl 'advice' texts from ncsa.or.th) , Contain too much WRONG
(dysfunctional) information:
https://library.mfa.go.th/elib/cgi-bin/um2.exe?
op=req&itemno=T026271&lang=0&db=Main&pat=cyber+security
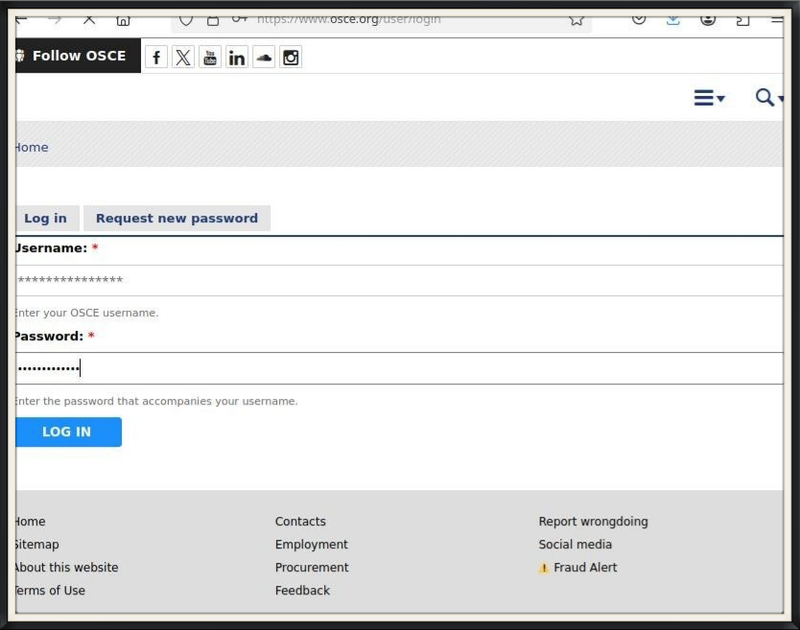
portal.mod.go.th
webmail.mod.go.th
library.mod.go.th
tts.dti.or.th/wp-admin *!*
apollo.mfa.go.th 122.0.0.80
fp.mfa.go.th
go.mfa.go.th
im.mfa.go.th
imap.mfa.go.th
library.mfa.go.th
ns1.mfa.go.th
ns2.mfa.go.th 122.0.0.13
nt.mfa.go.th 122.0.0.78
pop3.mfa.go.th
sd.mfa.go.th
smtp.mfa.go.th
ts.mfa.go.th
webmail.mfa.go.th 122.8.157.9 | 2405:f080:810:1f4:a57c:cc99:cb95:262c
www.mfa.go.th
.etc.
Creator : Budsarin Osataworanun
Create Date : 2023:10:16 06:19:37Z
Modify Date : 2023:10:16 06:20:54Z
Application : Microsoft Excel
*Doc Security : None
Titles Of Parts : ฐานข้อมูลข่าว, ฐานข้อมูลข่าว!_Hlk104820479, ฐานข้อมูลข่าว!_Hlk110276630, ฐานข้อมูลข่าว!_Hlk98703936
.etc.
---###---
The State accepts full liability for damage of any
kind resulting from the risks inherent in the careless electronic
transmission of messages.